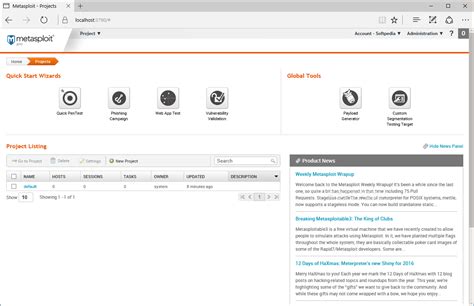
metasploit chanel 5 created | metasploit pro metasploit chanel 5 created Meterpreter is a Metasploit payload that supports the penetration testing process with many valuable components. Meterpreter will run on the target system and act as an agent .
Designer Disposable Face Masks – Tagged "Louis Vuitton" – TrayToonz. We have all different styles of designer and fun disposable face masks available! All regular surgical masks come in a pack of 20! All KN94 masks come in a pack of 10! All of these mask styles come with nose pieces. Quick view. Sale. Quick view. Sale. Quick view. Sale. .
0 · open source metasploit
1 · metasploit wikipedia
2 · metasploit pro
3 · metasploit interpreter
4 · metasploit encoder
5 · metaploit microsoft
6 · metaploit framework
Izvelkams plaukts apaviem Elite PL800mm, balts; 97,50. Izvelkamais plaukts apaviem Elite PL900mm, balts
In the process of learning Metasploit I haven’t been successfully able to create a session after completing an exploit. I started with Lame and haven’t been able to successfully .
Task 1 | Introduction to Metasploit. Metasploit is an open source tool that lets penetration testers enumerate, test and execute attacks, meaning this tool can help through all .
open source metasploit
metasploit wikipedia
The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. It is owned by Boston, Massachusetts-based security company, Rapid7. Its best-known sub-project is the open-source Metasploit Framework, a tool for . Metasploit is a popular open-source framework used by security professionals for developing, testing, and executing exploits against target systems. First created in 2003 by . Metasploit is an Open Source Penetration Testing Framework created by Rapid7 that enables security professionals to simulate attacks against computer systems, networks, . Meterpreter is a Metasploit payload that supports the penetration testing process with many valuable components. Meterpreter will run on the target system and act as an agent .
With the release of Metasploit 5, one of the most notable changes has been the addition of a new type of module type, the evasion modules. These new modules are designed . Section 1: Getting Started. Section 2: Metasploit Under the Hood. Section 3: The Hacking/Exploitation Process. Section 4: IoT Exploitation with Metasploit. Section 5: Post . By utilizing this robust framework, we can execute a wide range of actions, both essential and advanced. Furthermore, we will unravel the intricate capabilities of Meterpreter . In the process of learning Metasploit I haven’t been successfully able to create a session after completing an exploit. I started with Lame and haven’t been able to successfully use the exploit, although I managed to get Root by using CVE-2007-2447 exploit I found on GitHub.
Task 1 | Introduction to Metasploit. Metasploit is an open source tool that lets penetration testers enumerate, test and execute attacks, meaning this tool can help through all phases of a test. Metasploitable is an Ubuntu 8.04 server install on a VMWare 6.5 image with a number of vulnerable packages included, which can be run on most virtualization software. You can grab your copy at Vulnhub – Metasploitable. I used Kali .The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. It is owned by Boston, Massachusetts-based security company, Rapid7.
Metasploit is a popular open-source framework used by security professionals for developing, testing, and executing exploits against target systems. First created in 2003 by H.D. Moore, but in. Metasploit is an Open Source Penetration Testing Framework created by Rapid7 that enables security professionals to simulate attacks against computer systems, networks, and applications. Meterpreter is a Metasploit payload that supports the penetration testing process with many valuable components. Meterpreter will run on the target system and act as an agent within a command and.
With the release of Metasploit 5, one of the most notable changes has been the addition of a new type of module type, the evasion modules. These new modules are designed to help you create payloads that can evade anti-virus (AV) software on the target system. Section 1: Getting Started. Section 2: Metasploit Under the Hood. Section 3: The Hacking/Exploitation Process. Section 4: IoT Exploitation with Metasploit. Section 5: Post Exploitation. Section 6: Creating Custom Payloads in Metasploit. Section 7: . By utilizing this robust framework, we can execute a wide range of actions, both essential and advanced. Furthermore, we will unravel the intricate capabilities of Meterpreter while utilizing a plethora of transition words to seamlessly guide you through each command. In the process of learning Metasploit I haven’t been successfully able to create a session after completing an exploit. I started with Lame and haven’t been able to successfully use the exploit, although I managed to get Root by using CVE-2007-2447 exploit I found on GitHub.
metasploit pro
Task 1 | Introduction to Metasploit. Metasploit is an open source tool that lets penetration testers enumerate, test and execute attacks, meaning this tool can help through all phases of a test. Metasploitable is an Ubuntu 8.04 server install on a VMWare 6.5 image with a number of vulnerable packages included, which can be run on most virtualization software. You can grab your copy at Vulnhub – Metasploitable. I used Kali .The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. It is owned by Boston, Massachusetts-based security company, Rapid7. Metasploit is a popular open-source framework used by security professionals for developing, testing, and executing exploits against target systems. First created in 2003 by H.D. Moore, but in.
Metasploit is an Open Source Penetration Testing Framework created by Rapid7 that enables security professionals to simulate attacks against computer systems, networks, and applications. Meterpreter is a Metasploit payload that supports the penetration testing process with many valuable components. Meterpreter will run on the target system and act as an agent within a command and.
With the release of Metasploit 5, one of the most notable changes has been the addition of a new type of module type, the evasion modules. These new modules are designed to help you create payloads that can evade anti-virus (AV) software on the target system.
Section 1: Getting Started. Section 2: Metasploit Under the Hood. Section 3: The Hacking/Exploitation Process. Section 4: IoT Exploitation with Metasploit. Section 5: Post Exploitation. Section 6: Creating Custom Payloads in Metasploit. Section 7: .


metasploit interpreter
metasploit encoder
metaploit microsoft
metaploit framework
Make something up like the boss is immune to magic but creates a copy of himself(clones, simulacrum, artifact mirror images.) every round without all those resistances, perfect target for save or suck magic, fight ends when bbeg has no slot to duplicate himself and party melee users take him down with all copies destroyed.
metasploit chanel 5 created|metasploit pro